The Cloud Security Alliance (CSA), a leading IT trade association, has published its first report on risks and recommendations for connected-vehicle security, ahead of when driverless cars are about to see volume production in the near future.
The main idea behind the Observations and Recommendations on Connected Vehicle Security report is to describe potential vulnerabilities in self-driving and connected cars and to offer guidelines for preventing attacks.
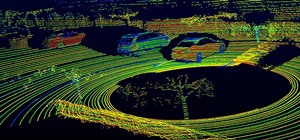
These guidelines will help to thwart attackers who may seek ways to access driverless cars' operating systems and networks. The classic entry point thus far has been through a car's controller area network (CAN) bus to install trojans or other malware software. For communications, black hat hackers could seek to intercept and alter GPS signals, mapping information, and other data self-driving cars receive to go from point A to B.
The CSA, whose members include Google, Microsoft, Amazon Web Services, HP, and Symantec; has issued a number of recommendations in its report. They include:
- Securing vehicles' designs and production processes by segmenting safety-critical from non-critical software and components. CAN bus connections, which have proved to be the main gateway for rogue access to vehicles' information systems in the past, must be encrypted. Separating the different CAN buses helps to improve security testing to detect and fix security holes. Separating CAN buses also helps to lessen the impact of a vulnerability if attackers will not be able to gain control of most of the car's functions through a single CAN bus.
- A vehicle's access to wireless access points (WAPS) must have improved encryption and configurations, and in general, must be made more restrictive than they have been in the past.
- While over-the-air (OTA) updates represent a potential wireless gateway for attackers to gain access to a car's driverless functions, the ability to immediately update vehicle software and to rollback those updates is critical. Wireless updates must also play a part during the entire lifecycle of components and software, beginning with the development stage.
- Systems designed to help improve traffic and payment information, such as when a car passes through tollbooths, mapping data is transferred to cars, or traffic flow and speeds are monitored, must be designed with security industry best practices.
- All vehicle components and software must adhere to a recognized national standards body's best practices, such as the US-based Department of Transportation's Security Credential Management System (SCMS).
Stealth Attacks
High-profile OTA attacks of Tesla's Model S and a Jeep Cherokee have underscored the urgency of creating a standardized approach to managing security risks of vehicles as they become more autonomous and connected.
In the case of the Tesla Model S, researchers demonstrated how they were able to install malware in the vehicle's telematics system with a laptop and then remotely bring the car to a stop by turning off its ignition. By exploiting a vulnerability in the controller area network (CAN) bus, a Chinese security firm was able to seize control of the braking, infotainment panel, door locks, and other systems on the Model S before Tesla patched the security hole with an OTA software update.
After WIRED detailed how the Jeep Cherokee's brakes, windshield wipers, radio, air conditioning, and other functions could be controlled remotely in 2014, Fiat Chrysler recalled 1.4 million cars and trucks, including 8,000 Jeep Renegades.
The Driverless Road Ahead
Carmakers are on the cusp of making and selling large-volumes of privately owned vehicles with advanced driverless capabilities. Audi is slated to become the first carmaker to sell Level 3 cars, but the A8's driverless capability will not be available for use pending legislation when the model goes on sale later this year. BMW plans to launch its first Level 3 model when its iNext is launched in 2021.
Daimler says its Mercedes S Class will offer driverless features for Level 2 self-driving for limited hands-off driving on highways.
Tesla's Autopilot software in the Model S currently offers Level 2 functionality, while the driver must remain ready to take back the wheel at all times along roads and highways and during lane changes in self-drive mode.
Meanwhile, as automotive software makers, component suppliers, and OEMs adopt more-stringent data security practices and protocols, researchers will be more challenged to discover and report vulnerabilities for the greater good of the security community. Malicious attackers will face more difficulties if they seek to seize control of cars for financial gain, through ransomware and other attacks, or worse still, in order to cause mayhem and harm.
Just updated your iPhone? You'll find new emoji, enhanced security, podcast transcripts, Apple Cash virtual numbers, and other useful features. There are even new additions hidden within Safari. Find out what's new and changed on your iPhone with the iOS 17.4 update.



























Be the First to Comment
Share Your Thoughts